Maximizing Cyber Security through Advanced Data Destruction Techniques
Maximizing Cyber Security through Advanced Data Destruction Techniques
Blog Article
The Value of Effective Data Destruction Practices in Shielding Sensitive Information and Ensuring Computer System Safety And Security
In a period where information breaches are increasingly usual, the relevance of efficient data devastation techniques can not be overemphasized. Organizations face significant risks when sensitive information is inadequately disposed of, potentially bring about unauthorized access and severe monetary repercussions. Implementing robust data damage methods not just mitigates these threats however also straightens with lawful conformity demands, making certain that companies maintain their track record and foster customer trust. The inquiry continues to be: what specific techniques can be employed to improve these practices, and how can organizations effectively incorporate them right into their overall cybersecurity structure?
Understanding Information Destruction
Comprehending information devastation is vital in today's digital landscape, where sensitive info can easily be compromised. Effective information devastation involves not merely erasing documents but making sure that information is irretrievable via extensive techniques. This procedure is essential for companies that deal with personal customer details, copyright, or inner documents, as any type of violation can lead to severe financial and reputational repercussions.
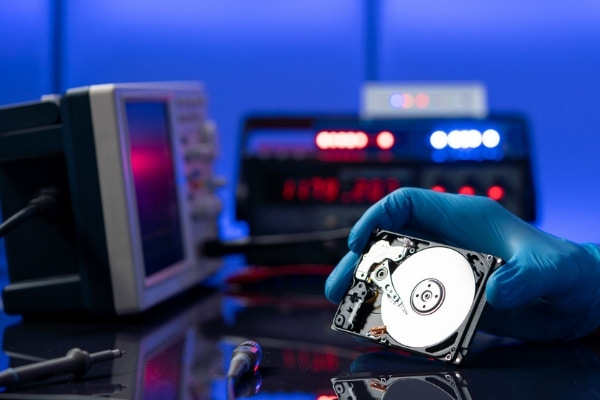
Data damage includes numerous methods, consisting of shredding physical media, degaussing magnetic storage space devices, and employing software-based services that overwrite data numerous times. Each approach offers a certain objective and has to straighten with the level of sensitivity of the info being dealt with. Physical damage is typically chosen for tough drives having very confidential information, while software approaches may be sufficient for less delicate info.
Furthermore, sticking to industry criteria and guidelines, such as the General Data Security Policy (GDPR) or the Wellness Insurance Coverage Portability and Liability Act (HIPAA), is essential for conformity and to reduce lawful dangers. Organizations must establish a durable data devastation policy, train workers on ideal techniques, and consistently investigate their treatments to guarantee that all delicate info is gotten rid of securely and efficiently.
Risks of Inadequate Practices
Insufficient information destruction methods expose organizations to substantial dangers that can have far-reaching repercussions. When delicate info is not properly thrown away, it continues to be vulnerable to unauthorized gain access to, which can bring about information breaches and identity theft. Such events not only endanger the security of individuals but likewise taint the organization's online reputation, resulting in a loss of client trust fund and possible economic repercussions.
Moreover, regulatory compliance is progressively rigorous in numerous industries. Failing to comply with data devastation guidelines can lead to hefty penalties and lawsuits against organizations. These charges can divert and strain monetary resources focus from core company operations.
On top of that, the abuse of recurring information can bring about copyright theft or company reconnaissance, threatening competitive advantages (data destruction). The impact of poor information destruction prolongs past immediate economic losses; it can additionally cause long-lasting damage to brand stability and market placement

Organizations must recognize that data safety and security is not solely regarding preventing violations; it also encompasses the accountable monitoring of information throughout its lifecycle. Neglecting reliable information damage methods can have devastating effects, emphasizing the need for durable steps to reduce these dangers.
Best Practices for Data Devastation
Executing reliable data damage techniques is crucial for guarding delicate details and maintaining conformity with governing standards. Organizations must embrace a multi-faceted strategy to guarantee that information is irretrievable, therefore stopping unapproved access and potential breaches.
First, data need to be classified based upon sensitivity, permitting organizations to use suitable devastation approaches customized to the degree of danger. For electronic data, using software-based data-wiping tools that abide by market criteria can effectively overwrite existing data. Physical damage techniques, such as shredding or degaussing, are critical for tools that save delicate details, guaranteeing full eradication.
Developing a clear information retention plan is crucial, detailing exactly how long different types of details ought to be retained before damage. Regular audits of data storage systems are additionally necessary to identify unnecessary or outdated data needing elimination.
Moreover, training employees on the value of information devastation and the certain methods to follow fosters a society of protection within the company. Preserving documents of information destruction refines provides accountability and supports compliance with external home guidelines and inner plans. By sticking to these ideal techniques, companies can considerably mitigate the dangers linked with information direct exposure.
Legal and Conformity Factors To Consider

Failure to follow these laws can lead to serious fines, including substantial penalties and reputational damage. Organizations has to carry out a robust data destruction policy that straightens with these legal frameworks and offers clear standards on the appropriate methods of data disposal, whether physical shredding or electronic wiping.
In addition, keeping documents of information damage tasks is important for demonstrating compliance during audits or inspections. By prioritizing legal and compliance considerations, companies can boost their data safety and security position and foster depend on with stakeholders and clients, ultimately adding to a more safe and secure information administration atmosphere.
Benefits of Effective Data Devastation
Effective information damage practices expand past mere conformity; they provide considerable advantages to organizations that prioritize them. By ensuring that delicate details is irretrievably damaged, companies alleviate the risk of data breaches and the possible economic consequences connected with them. This aggressive approach not only safeguards against unapproved accessibility but likewise improves the overall dependability of the company in the eyes of clients and stakeholders.
Implementing durable information destruction techniques, such as physical destruction of storage space devices or advanced information cleaning techniques, contributes to the strengthening of an organization's cybersecurity posture. data destruction. It lowers the possibility of copyright burglary and secures exclusive details, consequently preserving an one-upmanship out there

Final Thought
In final thought, efficient data damage methods are vital for protecting delicate details and enhancing total computer safety. Ultimately, a commitment to robust information damage techniques promotes a culture of responsibility, thus reinforcing a company's cybersecurity position and preserving client depend on.
Report this page